Using Let's Encrypt with IIS on Windows
Let's Encrypt is a new open source certificate authority that promises to provide free SSL certificates in a standardized, API accessible and non-commercial way. If you've installed SSL certificates in the past, you're probably familiar with the process of signing up for a certificate with some paid for provider and then going through the manual process of swapping certificate requests and completed requests.
Let's Encrypt is based on set of open service APIs that can be implemented on any platform and create certificates for Web servers including IIS. This seems like a fabulous idea, given that securing your site if you have any sort of authenticated access is an absolute requirement. It's not so much the money that's a problem since basic SSL certificates these days even from paid providers are relatively cheap (I use DnSimple both for domain management and SSL certificates), but the fact that you can completely automate the process of SSL creation and management is a huge win. This has both upsides and downsides actually and I'll talk about that at the end of the article. To be clear – I'm not a network admin and I don't have extensive experience managing certificates on a large number of sites so in this post I cover a few basic scenarios that I deal with in my own sites hosted on my own hosted servers.
Windows and IIS – not a first class citizen
I've followed the development of Let's Encrypt with interest, but there wasn't much to try initially as there was no implementation directly available for Windows. Last week I ran into Nik Molnar's post that points at some of the tools available for Windows using PowerShell, the Command Line and even the startings of a Windows UI based tool. Nik then goes on to describe an Azure plug-in implementation that can automatically register and renew Let's Encrypt certificates.
However I was more interested in the IIS pieces rather than Azure as I don't use Azure and host on IIS, so over the weekend I took these tools for a spin to see what's really involved in getting Let's Encrypt to work with my IIS sites. This posts is a summary of what I found.\
What's available on Windows
As is often the case with open tools, Windows is always the afterthought rather than the norm when it comes to open networking and security tools. So when Let's Encrypt initially went to beta there was no Windows support. However, now that it's been in beta for a while there are a few tools available that provide wrappers for the Automated Certificate Management Environment (ACME) API.
There are a number of options available:
LetsEncrypt-Win-Simple
Currently this seems like the easiest solution to getting new Certificates installed into IIS quickly and easily. This Windows Command Line utility includes an 'interactive' mode that lets you pick a host headered Web site on your server and will go out and create the certificate and install it into IIS in one seamless operation. This works great for manual installation or simple scripted installs. It's quick and easy and by far the easiest solution I tried so far.ACMESharp Powershell Commands
ACMESharp is a Powershell library that provides access to many (but not yet all) commands of the ACME API. Unlike the Win-Simple approach using the ACMESharp library requires a bit of scripting you have to write yourself with some logic, but you get a lot of control over the process and the ability to create and save the intermediate certificates.\Certify
This is a GUI implementation of the ACME API that promises to provide interactive ACME certificate management. Currently this tool is pretty rough, but improvements are coming and each new version seems to improve significantly. It's a great way to visually see certificates and obviously much easier for those that don't want to futz around with lots of command line foo.
To be clear, all of these tools are in very early release stages and so they are a bit rough with features missing… and that's to be expected. This stuff is new. Let's Encrypt itself is in beta and these tools build ontop of that base stack. But nevertheless I was able to use all of these tools to work to register certificates so you can get started today using Let's Encrypt on your own IIS Web sites.
What's missing in all tools currently is administration. You can't revoke or remove certificates and there's no way to clear out certificates on the remote servers. While testing I ended up hitting a limit of certificates registered on one of my sites and then couldn't go further with that site as I can't remove/revoke any of the certs. Natch.
Because of this, I recommend if you plan to play with these tools, create a new host headered test site or sites with valid internet accessible domain names and play with that site before you update and add certificates to any live sites you care about. Once you figure out how things work it's easy to get certificates installed on a live site.
The Easy Way: LetsEncrypt-Win-Simple
By far the easiest way to create and install a new certificate is LetsEncrypt-Win-Simple. This tool runs from the command line and has a few very easy to understand options. Basically you pick a site from the list of active Web sites using host headers on your server and the utility goes out and creates a certificate for you, creates an https binding and attaches the certificate. If there's already a certificate there the certificate is replaced with the new one.
This tool is basically wrapping up all the intermediate steps of creating a registration, domain and certificate. When you run again later it uses the existing store to retrieve the existing registration and domain information to run a renewal. You don't need to know anything about how the ACME API works or the pieces involved which is nice. Actually I wish I would have looked at this tool first before digging into the lower level tools as I did.
Installation is easy: You can install the latest version from their GitHub Releases page and simply unzip the zip file into a folder. The zip file contains a single .NET executable Console application and the required SSH native debpendencies plus a couple configuration files.
To run it, simply open a command window, CD to the install folder and run:
LetsEncrypt
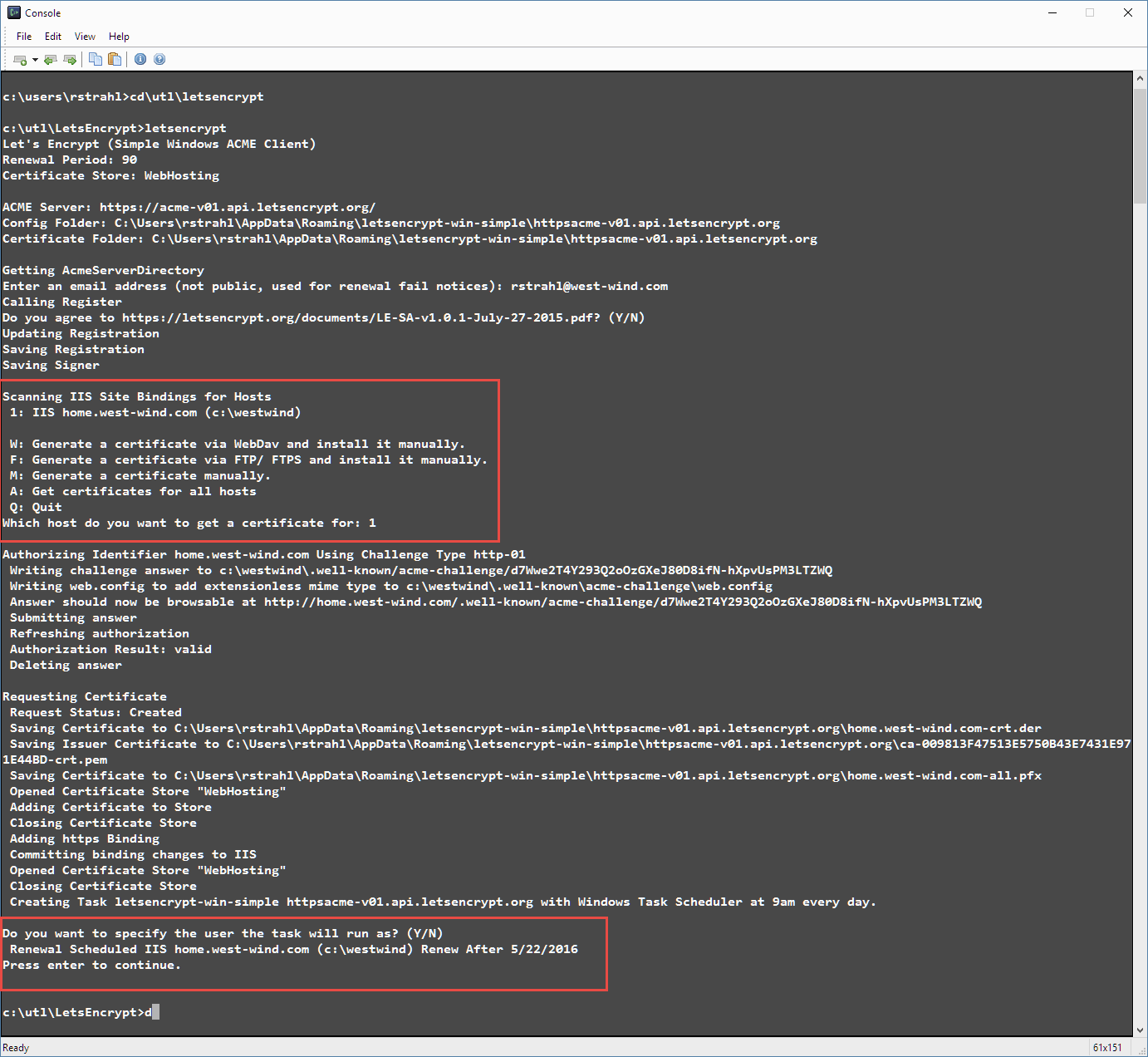
Here's what the interaction looks like (on my home machine which only has one host-headered site I added for testing):
(note that the site you're using here has to be internet accessible and you have to run these tools from the machine that will receive the certificate)
If all goes well, you'll end up with a new certificate installed in IIS on the Web site you specified.
If an existing certificate is installed it will be replaced with the new one. The utility is smart enough to detect existing Let's Encrypt certs and removes the old one and replaces it with the new one leaving only the new one in place. Any other certificates are simply left in place, but are not unbound.
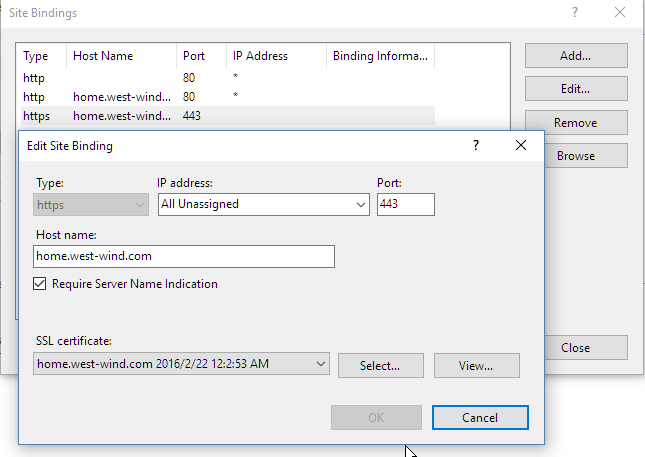
SNI – Multiple SSL Certificates per IP Address
Note that IIS by default allows only binding of a single SSL certificate to an IP Address. Starting with Server 2012 IIS support Server Name Indication (SNI) which allows you to bind multiple SSL certificates to a single IP Address. In order for this to work you need to make sure that every site using the same IP Address has the SNI flag checked as shown above. SNI binds the certificate to a host header rather than the IP Address. Note there are issues with SNI support for old versions of IE on Windows XP which won't properly navigate the SSL signature. If that's a problem you will need to stick with IP Bound SSL certificates.
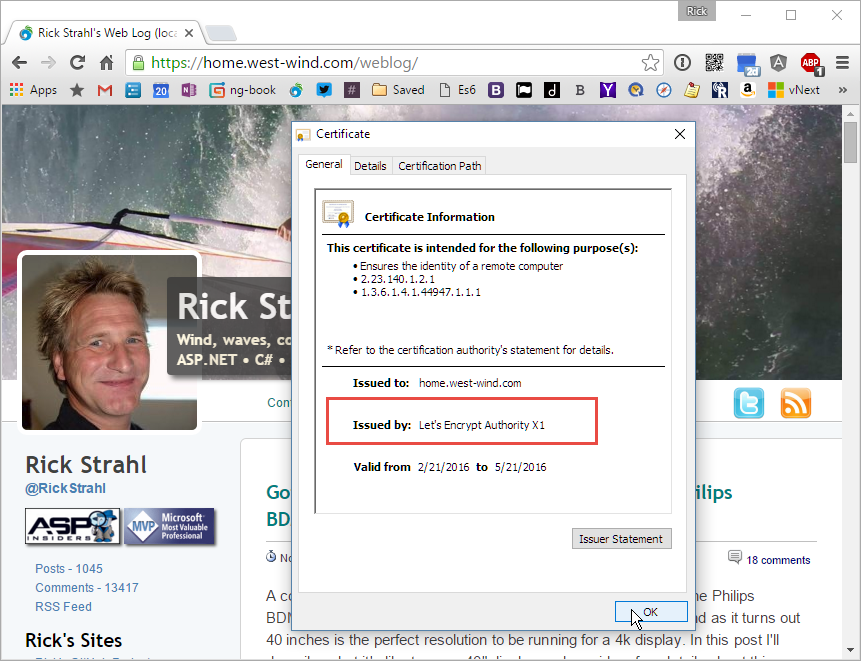
If you open the site in a Web browser you can quickly check to see if the certificate is working, by clicking the secure icon and checking the certificate information. As you can see the certificate is the one created by Let's Encrypt.
What's nice is that you can simply re-run LetsEncrypt and it will go out and create a new certificate and remove the old one, so at any time when you need to renew/revoke it's quick and easy to update the certificate as needed.
Yay! This process is pretty straightforward and simple. LetsEncrypt-Win-Simple also has a few command line options that let you automate the domain to create the certificate for and disable prompts so you can automate this process as well. As the name implies LetsEncrypt-Win-Simple is simple without having to understand the gory details of how Let's Encrypt works behind the scenes and unless you have specific needs beyond registration this is the way to go IMHO.
Renewals
LetsEncrypt-Win-Simple also includes an interface to renew all certificates easily. You can run:
LetsEncrypt --renew
and it checks all sites it's managing for expiration dates and if expired (or on the day of expiration) it automatically renews and replaces the old cert with a new one. Nice!
The utility also creates a scheduled task that runs this command once a day and fires update requests. Note you might have to tweak the task User Identity settings as described here to ensure that the user is logged on properly when running the scheduled task. Note that the user is the logged on user because this tool creates the Let's Encrypt vault in a %appdata%\letsencrypt-win-simple which is a user specific profile. It'd be much better if the vault was in a global location like \ProgramData so it can run under any account including system accounts. But that's a minor issue.
More Control with ACMESharp and PowerShell
If you want to work with the lower level ACME APIs directly and you want fine grained control over the cert creation process then ACMESharp's Powershell commandlets are a good way to do it. It's all based on a .NET library that provides the core interface to the ACME APIs so you can also automate your own applications.
LetsEncrypt works with a few core concepts:
- A registration which is essentially an entity that's creating certificates (you or your company)
- An identifier which is the domain name you are registering
- A Certificate tied to that domain name
The process involves creating a registered account once, then creating multiple domains that can be registered. Each domain then can have multiple certificates associated with it over time.
The ACMESharp GitHub site has a pretty good topic on how to get started that I was able to get going with that goes through the process of setting up a registration, setting up a domain and then creating the actual certificate.
Be forewarned – there are quite a few steps and the steps change if you're doing a renewal – it's not as simple as LetsEncrypt-win-simple although you can build something similar with ACMESharp (as LetsEncrypt-win-simple does as it uses the ACMESharp APIs). ACMESharp is a lower level tool that provides the API surface that you can build on top of.
But you can relatively easily use the Powershell interface to create new and renewal certificates. The process through these steps changes depending on whether you're doing a first time installation where you have to create the initial registration and domain or a renewal where you simply need to add a new certificate to an existing domain registration.
After quite a bit of experimenting with temporary domains I ended up with a parameterered Powershell script that I now use to register and update domains with. You might find this useful in addition to the instructions (for one thing it's easier to cut and paste from if you do want to do the steps manually).
#install-Module -Name ACMESharp
import-module ACMESharp
$email = "mailto:rick@east-wind.com"
$domain = "codepaste.net"
$alias = "codepaste"
$iissitename = "codepaste.net"
$certname = "codepaste$(get-date -format yyyy-MM-dd--HH-mm)"
$pfxfile = "c:\Admin\Certs\$certname.pfx"
$initializevault = $FALSE
$createregistration = $FALSE
$createalias = $TRUE
# Change to the Vault folder
cd C:\ProgramData\ACMESharp\sysVault
# First time on the machine - intiialize vault
if($initializevault)
{
Initialize-ACMEVault
}
Get-ACMEVault
if($createregistration)
{
# Set up new 'account' tied to an email address
New-AcmeRegistration -Contacts "$email" -AcceptTos
}
if($createalias)
{
# Associate a new site
New-AcmeIdentifier -Dns $domain -Alias $alias
# Prove the site exists and is accessible
Complete-ACMEChallenge $alias -ChallengeType http-01 -Handler iis -HandlerParameters @{WebSiteRef="$iissitename"}
# Validate site
Submit-ACMEChallenge $alias -ChallengeType http-01
# check until valid or invalid - pending
Update-ACMEIdentifier $alias -ChallengeType http-01
Update-ACMEIdentifier $alias -ChallengeType http-01
}
# Generate a certificate
New-ACMECertificate ${alias} -Generate -Alias $certname
#Submit the certificate
Submit-ACMECertificate $certname
# Hit until values are filled in
update-AcmeCertificate $certname
pause
# Export Certifiacte to PFX file
Get-ACMECertificate $certname -ExportPkcs12 $pfxfile
Note that by setting the 3 boolean values you can control the flow for new and renewal certificates. The way the script is set up above it runs for a certificate renewal/update.
This script produces a PFX file which can then be imported into IIS. There are also tools to install and update existing certificates into IIS but it looks there are currently some changes in the API that made this not work for me. I wasn't able to even get the tools to load.
You can manually install the certificate with:
certutil -importPFX "c:\admin\certs\codepaste2016-02-28--20:22" –p password
or manually import it from the IIS Management Console and the IIS Certificates section. This works well for first time installs, but if you need to update an existing certificate then you still need to swap the certificates in IIS using the Management Console or command line tooling.
Certify – A Let's Encrypt GUI in the Making
(updated March 10th, 2016)
Certify is a visual GUI based tool that is also based on the ACMESharp library and provides a visual management interface to certificate operations. This tool is currently in Alpha and it's very rough – in fact when I initially tried it a few weeks back I wasn't able to actually get a certificate to create. However there's been a recent update that now has the basic features working even though the UI is still a bit rough.
The Certify UI pretty much reflects the terminology of a Vault, contact (email really) and domains and certificates and the UI reflects this hierarchy. You can create new domains and then attach new certificates to each domain. You can also use this UI to renew, export and apply the certificates directly into IIS Web Site bindings.
The tool lets you create a new email contact, and then lets you add domains and certificates interactively. You can issue a new certificate. The certificate takes a minute or so to get generated and currently you have to refresh the Vault to see the updated, validated certificate. Once validated you can use Auto Apply to pick a Web Site and port to bind the certificate to. You can also export the certificate to a .pfx file, and you can ask to renew the certificate with Certify at any point.
This tool is clearly in Alpha stage, and while it doesn't work yet, it's nice to see a UI for this. Having a visual view of installed certificates and seeing status of certificates at a glance can be useful. It would be nice to see different colors based on the expiration state of certificates (red for expired, orange for a couple of weeks, green for valid) etc. Having a UI to see everything at a glance is really nice.
Keep an eye on this tool going forward.
Where are we?
The idea of free and open source SSL certificates is certainly coming at the right time as we are looking at a big push from Google and other big Internet players to try and enforce SSL on every Internet connection. Running SSL can help prevent many HTTP, XSS and man in the middle type attacks by encrypting content and headers. Even though SSL certificates have gotten significantly cheaper, having an easy and 'official' way to create SSL certificates is going to do wonders to increase SSL usage. I know I have a handful of small side project sites that I can't justify spending even $20 a year for SSL on, but if it's free – hey, why the hell not.
It's not just about free certificates either – the fact that the certificate generation can be completely automated is also appealing especially with those that have large numbers of sites and certificates. Being able to check certificates once a day for expiration and renewing when within a day to keep things current makes for one less thing to worry about.
One issue that I see with Let's Encrypt in the current state of the tools is that certificates are valid for a maximum of 90 days or 3 months. This means you need to manage renewals much more frequently than your typical 1 year certificate. Let's Encrypt supposedly has mail notifications in place if certificates expire, but I haven't been able to try that out yet as the expirations are too far in the future. Automation of the renewal process is going to be key here – nobody will want to have manually renew certificates or even be notified every 3 months. I have 5 certificates on my Web server today and even a year for expiration is a big hassle as these certificates expire at different times of the year. To me the automation aspect is much more relevant than the cost.
Let's Encrypt itself is still under development and the Windows tools are even less mature. The base API exists and can be used today to create certificates as I've shown here, but there's a lot of work still to be done. The certificates created currently are the most basic certificates you can get. There's no support for wildcard certs, or higher end validated certs. It's not clear whether that will be supported in the future as setting up registrations for these types of certificates is much more involved. So today Let's Encrypt is not a solution for all SSL needs, but it definitely serves the low end sector well. And you definitely can use it today to get free SSL certificates if you're willing to put up with a little bit of growing pain. Especially using LetsEncrypt-win-simple it's pretty easy to get started and even keep things up to date.
In the future I hope we will see integration for services like Let's Encrypt directly built into Web servers. Having a common protocol for certificate registration seems so obvious in hindsight. Especially for IIS and Windows in general which has always been such a pain in the ass with certificate management. I suspect that we'll see this sort of integration sooner rather than later.
How do you see yourself using this service? Would you use it just because the service is free, or because of the automation opportunities? Sound off in comments.
Resources
- Code Magazine Article: Securing IIS Web Sites with Let’s Encrypt Certificates
- Moving to Lets Encrypt using Certify
- LetsEncrypt-Win-Simple
- ACMESharp Powershell Commands
- Certify The Web
- Let's Encrypt on Azure (Nik Molnar)
Other Posts you might also like
The Voices of Reason
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
Sensible ways of doing this are long overdue. Hopefully there'll be a production ready API and decent cert lifetimes soon.
# re: Using Let's Encrypt with IIS on Windows
I'm completely with you: SSL is a must, but SSL is a PITA...
I already use free certs (from StartSSL), but each year I'm confused and it still takes some hours at least to renew the certificates of the websites I host on my IIS server. I'm going to try Let'sEncrypt-Win-Simple and ACMESharp Powershell Commands on a spare domain name and if all works out fine I'll automate the renewal process for *real websites*
Thanks again!
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
Question...
What is the issue about not being able to revoke or remove teh certificate once it is issued? Is it something to be really concerned about?
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
This could be caused by IIS not being setup to handle extensionless static
files. Here's how to fix that:
1. In IIS manager goto Site/Server->Handler Mappings->View Ordered List
2. Move the StaticFile mapping above the ExtensionlessUrlHandler mappings.
(like this http://i.stack.imgur.com/nkvrL.png)
3. If you need to make changes to your web.config file, update the one
at C:\Users\rolando\Desktop\letsencrypt-win-simple.v1.9.0\web_config.xml
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
It's possible to set up a server hosted mechanism for this. It'd be nice if a Web based front end could be built to do this - that way you could remotely manage the certificates. Nothing for this yet, but I bet somebody will build this.
# re: Using Let's Encrypt with IIS on Windows
thanks for another great post of yours. I really appreciate the time and effort you put into your research and writing. Your blog is always worth a visit - if it's on Google's first result page that's where I go first for the information I'm looking for.
Keep it up, I'm convinced many other readers appreciate your content at least as much as I do.
Btw, this post helped me quickly set up a TLS certificate in IIS on windows just yesterday :-)
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
LetsEncrypt-Win-Simple also includes an interface to renew all certificates easily. You can run:
LetsEncrypt --renew
and it checks all sites it's managing for expiration dates and if expired (or on the day of expiration) it automatically renews and replaces the old cert with a new one. Nice!
The utility also creates a scheduled task that runs this command once a day and fires update requests. Note you might have to tweak the task User Identity settings as described here to ensure that the user is logged on properly when running the scheduled task.
The problem is I cannot find any LetsEncrypt scheduled task, should I create one, and which application should I choose?
# re: Using Let's Encrypt with IIS on Windows
"At some point in the future I intend to add auto renew as a service to the app. Until then though you could use the ACMESharp powershell scripts (which Certify uses) to script any action you like including renewal."
I'm hoping he develops something soon since Certify has been the easiest way to generate certs so far.
# re: Using Let's Encrypt with IIS on Windows
I've actually stepped back from Certify and I'm now using LetsEncrypt-win-simple which seems to be working better with renewals. Recent updates have also made this process much more seamless to get the certs created.
I wish I had time to help out with Certify - it seems such a shame that the project is largely abandoned by the developer (for the same time constraints). It'd be so nice to have a visual way of doing this in addition to the ACME library based solution.
# re: Using Let's Encrypt with IIS on Windows
Daniel Smith
@databee
# re: Using Let's Encrypt with IIS on Windows
Thanks for this article, great help.
Have you found a way to use the LetsEncrypt Win Simple manually and automatically add the IIS binding afterwards? Seems like you have to use the --script param somehow?
We basically want to have a go-live process which runs the LetsEncrypt Win Simple manual command and then ensure that a IIS binding / cert is applied for that site.
Possible? I see you've written an article about PowerShell, but can't quite see how to tie it all together. Any help greatly appreciated!
Dave
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
# re: Using Let's Encrypt with IIS on Windows
Thanks a lot for this post. I used LetsEncrypt-Win-Simple and got my site with a valid certificate in 5 minutes!
I have updated the scheduled task with my local admin user to also work when not logged in. Works like a treat.
The last step for me is now to redirect the HTTP site to HTTPS and let Google know about it.
Really cool, thanks.
# re: Using Let's Encrypt with IIS on Windows
We've tested successfully and published a video for both the Lets-encrypt-simple client and the ACMESharp PowerShell Module.
The Lets-encrypt-simple client seems to be more suitable for installing single domain certificates on Windows servers running IIS. The video instructions are available here:
http://www.netometer.com/blog/?p=1758
The ACMESharp PowerShell module is perfect for the automatic installation and renewal of Exchange Multiple Domain (SAN) certificates - the video demo is available here:
http://www.netometer.com/video/tutorials/How-to-Install-LetsEncrypt-Certificate-in-Exchange-Server
In the demo, we are scheduling a task in task scheduler to renew the Exchange certificate and it works flowlessly.
Regards,
Dean
# re: Using Let's Encrypt with IIS on Windows
Hi.
Thanks much for the post on Let's Encrypt. I am now using LE for a company home page. However, I want to redirect all HTTP traffic to the HTTPS protected web site, and from what I understand, LE uses HTTP to request renewals? Will such a redirection cause issues with the automatic renewal?
Thanks much for any suggestions / help! Walt
# re: Using Let's Encrypt with IIS on Windows
Walt - I use https redirects and it seems to work. I think for the first registration it has to be http, but for renewal https requests seem to work for me.
# re: Using Let's Encrypt with IIS on Windows
Great article, Rick. Been looking for the best way to do this with IIS going forward. This appears to be the best method at this point. Thanks for digging into it and sharing.
# re: Using Let's Encrypt with IIS on Windows
Hi
I am trying to do my first renewal but when I use LetsEncrypt --renew it tells me that my cert can't be renewed as it is still valid but when I go to my website my cert has expired.
Any else have this issue? I have 2 sites that are using ssl on my site. I checked Require server name identification.
# re: Using Let's Encrypt with IIS on Windows
Thanks, I can't believe how easy that was... all those years of struggling.
# re: Using Let's Encrypt with IIS on Windows
Xiao, did you fix the issue you had with the renewals ? if so, what did you do to fix it ?
# re: Using Let's Encrypt with IIS on Windows
Thank you for the Information. I had previously given up trying to install these certificates and converting them to IIS7. The Easy Way: LetsEncrypt-Win-Simple was actually the fastest and easiest for me.
Thank you 1000x time.
Mike
# re: Using Let's Encrypt with IIS on Windows
@Rick Strahl : Walt - I use https redirects and it seems to work. I think for the first registration it has to be http, but for renewal https requests seem to work for me.
https redirect works well for renewal but what will happen when expiration date is reached ? the script handles that with submitting a new challenge request but it might need to do a http request as for the 1st run.
What do you think about it ?
# re: Using Let's Encrypt with IIS on Windows
@Guilliaume - I know it works because I have LetsEncrypt-WinSimple handle auto-renewals for me on a couple of sites that auto-redirect to https. I think it's only the first registration that has go over http even if a cert is already installed.
# re: Using Let's Encrypt with IIS on Windows
Rick,
I think it's only the first registration that has go over http even if a cert is already installed.
After you create a LE account (that's the first thing the client does) and a private/public key pair which is used for encrypting the communication with LE servers, the registration of the domain names that you need to have included in the certificates is performed, and a successful domain name registration (http-01 validation) with LE is valid for slightly longer than 11 months.
That explains why you don't see http subsequent validations from LE during the certificate renewals while the registration of the Domain Names is still valid - in 12 months, you'll have to perform a new registration (validation) of the names again.
Regards,
Dean
# re: Using Let's Encrypt with IIS on Windows
Hey Rick!
Great tutorial that you set up here!
I don't find the switch for "including the www." to the certificate. So do I have to install 2 certs for www. and without www. in windows (?) because Plesk on Linux offers the option to do that by cheching a box. Is that a limitation doing that under windows?
Thanks for any help!
Best regards
Niko
# re: Using Let's Encrypt with IIS on Windows
@Niko - yes you have to set up each individual subdomain include www.mydomain.com and mydomain.com.
# re: Using Let's Encrypt with IIS on Windows
@Rick Thank you! That means I have to install in this case really 2! certs?
# re: Using Let's Encrypt with IIS on Windows
@Niko - yes, but because you can have certificates auto-renew themselves, having two certificates is really not a problem.
# re: Using Let's Encrypt with IIS on Windows
Hi, Rick many thanks for the script utility. Is it possible to get a cert for subdomain like ssl.mysite.com?- the utility can't find IIS site with subdomain bindings. Best regards, Andrew
# re: Using Let's Encrypt with IIS on Windows
@Andrew - that definitely works. Make sure you can see the sites in the IIS Manager. When you run LetsEncrypt-WinSimple it should see and show those sites. Make sure you're running as an Administrator, otherwise you won't have access to the admin objects required to enumerate the Web sites. You also need to make sure you use SNI for each site.
# re: Using Let's Encrypt with IIS on Windows
Hi Rick
This is a good write-up, thanks.
I am currently setting up a site with two web servers behind Cloudflare loadbalancing (which is still in preview).
I am attempting to set up SSL for these servers using LetsEncrypt-Simple. However, authorisation is failing for server X, since the load balancer is probably routing the request for the answer file over to server Y, and vice versa.
So, my questions are as follows:
- How can I set up SSL for all of my web servers behind the load balancer?
- How would we configure the renewal process for this scenario?
Thanks
# re: Using Let's Encrypt with IIS on Windows
Hi Rick, again a question from me.
All the first time installed certs have a duration of 90 days. How many days before expiration date will the scheduled task renew the certs?
( I also modified the automated installed scheduled task job, that runs every day at 9 o'clock a) run with highest privileges b) run also when user is not logged in (admin password is set), because it should run without a logged in administrator.)
Many thanks and regards
Niko
# re: Using Let's Encrypt with IIS on Windows
I keep getting this error when refreshing through letsencrypt:
The ACME server was probably unable to reach http://www.mydomain.com/.well-
known/acme-challenge/
I followed the steps listed, but to no avail. Any other suggestions to look at?
# re: Using Let's Encrypt with IIS on Windows
@Ben - You have to ensure that server affinity is guaranteed and that when you set up the request it is guaranteed to go back to that very same machine when Lets Encrypt calls back since that machine will be the only one that has the request info to verify. Most likely you have to take the site off the load balancer or run balancer with a single site enabled to make this work. Otherwise - you need to use a traditional route for getting a certificate which is more complicated but doesn't require live validation of the running site.
# re: Using Let's Encrypt with IIS on Windows
Caddy is a web server with native integration with Let's Encrypt, https://caddyserver.com/.
# re: Using Let's Encrypt with IIS on Windows
My question of 18 April is still unanswered. Somebody should have made experiences because Letsencrypt is not new but for me a relative new theme. Maybe somebody has an answer for me, when the scheduled task job makes the renew earliest? Thanks and regards Niko
# re: Using Let's Encrypt with IIS on Windows
@Niko - I'm not sure exactly when LetsEncrypt starts the renewals, but I believe it's at 60 days. All I know is that my renewals just happen automatically with (AFAIK) no hiccups of downtime due to missed renewals.
# re: Using Let's Encrypt with IIS on Windows
Hi Rick great article! HUGE fan of lets encrypt it is like something i never knew existed but desperately need! I am using asp.net core with a reverse proxy (not the aspcore IIS module) - this doesnt play nicely with the auto-renew as you need to disable the reverse proxy (unless your proxied app runs in the same folder as your IIS web application)
fortunately you can do this before the renewal runs via command line:
Import-module webadministration
set-webconfigurationproperty '/system.webserver/rewrite/rules/rule[@name="ReverseProxyInboundRule1"]' -Name enabled -Value false -PSPath "IIS:\sites\<your_website_name>"
# re: Using Let's Encrypt with IIS on Windows
Hey Rick,
Thanks for your write-up about LetsEncrypt-Win-Simple.
I managed to get it working within IIS 8. This is going to simplify an annoying task.
However, when asked if I want to to auto renew every 60 days I chose 'No' as I thought I could choose 'Y' the next time but it does not give me this option again. I see there is a new letsencrypt daily task in Task Scheduler but I don't think this is the 60 day auto renewal.
I do not see a way to either renable the auto renewal Y/N option when running letsencrypt.exe or how to manually add it to a config file.
Just wondering if this is something you know about?
Thanks
# re: Using Let's Encrypt with IIS on Windows
Great post. I read your posts years ago when I was learning ASP.NET developing. Your posts helped me a lot. And this post helped me a lot again. Thank you. 谢谢。
# re: Using Let's Encrypt with IIS on Windows
@Kit - every time you renew, Lets Encrypt Win Simple will prompt to recreate the scheduled task. The scheduled task runs through all sites. In theory you need to only set this up once and then answer no on subsequent requests just in case you made changes (like the account it runs under). The renewals will still fire. The renewal tasks fires once a day, and it does some check for the certificate expriation date before it expires. Exactly when it checks and decides to renew I'm not sure - you'd have to look at the source to see what they do exactly in the scheduled task operation (--renew).
# re: Using Let's Encrypt with IIS on Windows
ISTR the Windows scheduled renewal task runs every 24hrs but only actually renews the cert when it needs to. It's a hidden task and runs let'sencrypt with these flags.. --renew --baseuri "https://acme-v01.api.letsencrypt.org/"
# re: Using Let's Encrypt with IIS on Windows
and another one for you Rick....
As we all know - or have figured out - generating certs requires port 80 and 443 to be open [although possibly only 443 once an account has been set up for renewals..]. So I've been looking at the DNS-01 challenge which would save (in my case) messing with perimeter firewalls, IIS not using port 80 and having to switch anonymous authentication on to generate or renew a cert.
Does -Letsencrypt-win-simple support this do you know and do you have any tips?
TiA
David
# re: Using Let's Encrypt with IIS on Windows
I am not able to create a new SSL to my default SSL site.
My "Default Site" is listening to all http:80 requests on all addresses.
I tried setting up an SSL binding with SNI, and LetsEncrypt didn't pick up on it.
I created a default SSL site (was getting a warning in IIS) by creating an HTTPS binding on all IPs with no host name indicated.
This didn't work.
I tried creating a new site with SSL bindings to both the hostname and no hostname (both with all and single IPs), but this didn't work.
What could I be missing here?
# re: Using Let's Encrypt with IIS on Windows
You have to bind to a specific domain name so the site has to be set up with host headers and EACH host header has to have its own certificate. If you have existing bindings or a wildcart cert then it won't work.
Use LetsEncrypt-WinSimple and look at the list it produces and if it doesn't pick up your site it's not configured properly for Host Header/SNI/Bindings.
# re: Using Let's Encrypt with IIS on Windows
Finally got mine working after getting my bindings corrected and ports opened. Then, used Certify.
# re: Using Let's Encrypt with IIS on Windows
Had no idea IIS would reverse proxy and that there were LetsEncrypt clients. Bang up article!
For idiots like me you might add the "ran as admin" part to the main article text about win-simple.
# re: Using Let's Encrypt with IIS on Windows
Hi
Is it really (still) not possible to have one SSL certificate for multiple domain aliases / sub domains? I ask because on my Synology NAS this seems to be possible without any problem and works automatically as it should... There is an input for aliases when creating the request.
Will have a look on certify t. w. now but isn't free anmyore and doesn't even offer one time purchase!
Thx & regards
# re: Using Let's Encrypt with IIS on Windows
@Fix - Sure you can have a wildcard certificate on IIS, but Lets Encrypt does not create them. You need to use some other provider to get a wildcard certificate. According to Lets Encrypt wildcard certs are coming next year.
# re: Using Let's Encrypt with IIS on Windows
Hi,
I created a fully automated PowerShell script based on this article. It automates the process of requesting a Certificate and assigning it to an IIS Site. It can also handles renewals.
https://github.com/GLubomirov/Lets-Encrypt_Automate_PowerShell
Thanks for this article. Hope my script will help you guys too.
Have a great day, George Lubomirov
# re: Using Let's Encrypt with IIS on Windows
@Georgi - that's awesome!
# re: Using Let's Encrypt with IIS on Windows
Hello, we would like to use Let's Encrypt for several of our hosted IIS 7.5 sites, we do not use host headers but rather bind to a specific IP address on port 80. The IP address used is an INTERNAL one we have assigned via our firewall mapping that corresponds to the client's actual domain IP address. We are struggling to find a tool that will work for us.. I know Certify won't. Can you suggest a solution for us?
# re: Using Let's Encrypt with IIS on Windows
@Vicky - Lets Encrypt uses domain validation which means the domain has to be visible to the public to verify ownership. Basically you have to run LE on a server that responds to that domain.
So you can't use it unless you expose your IP to the Internet. Perhaps you can do it temporarily to get the certificate and then close if off again, but then Updates also won't work (unless you open it up again).
# re: Using Let's Encrypt with IIS on Windows
I tried the LetsEncrypt-Win-Simple, but it doesn't seem to work for my WordPress website installed on IIS 8 😕
# re: Using Let's Encrypt with IIS on Windows
Thanks Rick, our clients domains are visible to the internet using the external IP assigned in their DNS records.. we map their external IPs to internal IPs on our firewall/gateway and use the internal IPs in our Binding. I was hoping a tool like Let's Encrypt Win Simple would let us request an LE cert using the external IP somehow since we don't use host headers.
# re: Using Let's Encrypt with IIS on Windows
@Vicky - The domain needs to be publicly visible without any special DNS configuration as Lets Encrypt will send messages to your domain to verify. You don't need host-headers but if you don't use them (and SNI in IIS 8 and later) then each cert requires a dedicated IP address.
# re: Using Let's Encrypt with IIS on Windows
@Jwan - not sure how Wordpress handles the certificate URL requests. Basically Lets encrypt calls special URLs on the site and while LE-WS should set up config it's still possible that the site overrides URL management.
I think you can probably find more info on how to use LE certs with Wordpress in general with custom plug-ins for Wordpress.
# re: Using Let's Encrypt with IIS on Windows
Just used Certify as of March 1, 2018 and it worked flawlessly. Very easy and nice.
Thanks for the great article and helpful content.
# re: Using Let's Encrypt with IIS on Windows
IIS8 and above has option called Central Certificate store where in you need to put pfx file of there certificate on specific path and need not to install certificate.
does anyone know if this is something supported by lets-encrypt including install and auto-renewals.
# re: Using Let's Encrypt with IIS on Windows
Information has been a life saver. I got 60 sites on one production server updated quickly. My issue is that I have 2 productions servers behind a hardware load balancer. I have a 3rd web server for staging. Normally all changes are made on my stage server and pushed to my 2 production servers. I cannot run lets encrypt on my staging server since it doesn't really host the sites
I run letsencrypt on one of my production servers. I then export the certificates to my stage server. On the stage server I bind the certificate to the site. I then push everything back to the 2 productions servers. The only way I can think of making this easier is to run letsencrypt on both production servers and let the scheduled task renew certificates on both servers. In this case my production servers would have certificates with different keys.
Is there a simpler approach I should be looking at?
# re: Using Let's Encrypt with IIS on Windows
I know this is an old thread, but after a few years of using Win-simple, it is now failing to add or renew a certificate for one of my websites. I also tried Certify and had similar errors. From Win-simple...
[INFO] Plugin IISBinding generated target [IISBinding] yyyz.net (SiteId 21) [ @ C:\WebSites\yyyZLtd\wwwroot] [INFO] Authorize identifier: yyyz.net [INFO] Authorizing yyyz.net using http-01 validation (SelfHosting) [INFO] Answer should now be browsable at http://yyyz.net/.well-known/acme-challenge/LeSrNar5ASGN8NikDQQpyqhc05kCT5itxtrAkoKpSKs [EROR] Authorization result: invalid [EROR] NullReferenceException: Object reference not set to an instance of an object.
Any suggestions or guidance?
# re: Using Let's Encrypt with IIS on Windows
Great post by the way!
Have you ever tried using lets encrypt on a web farm environment that utilizes a "Shared Configuration"? Example: 6 web servers hosting the same sites and they get their content and configuration on 1 shared location.
Thanks for any comments!
# re: Using Let's Encrypt with IIS on Windows
Thanks Rick, but your site is currently showing a grey information icon for me. When I click it, it tells me that my connection to this site isn't entirely secure.
I'd like my own website to be a full blown greenie if I install an SLL. Any idea as to what might be the cause of the grey icon?
# re: Using Let's Encrypt with IIS on Windows
Great article! I have just used Certify to add an SSL certificate for a IIS based website in less than 10 minutes.
# re: Using Let's Encrypt with IIS on Windows
THANK YOU! I just started using the CertifyTheWeb.com app to add SSL for three IIS based sites. It is a breeze! Just what I needed.
# re: Using Let's Encrypt with IIS on Windows
Really useful - thanks so much for this post. IIS certificate installation completely painless. Your blog now bookmarked!
# re: Using Let's Encrypt with IIS on Windows
Hello, I'm working with your script for over one year. It is working well! There is one thing I would like to know: I have some sites which are secured with comodo certificates. Today a customer called me that the SSL binding was down. The script had renewed a LetsEncrypt certificate instead of the customers comodo cert but did not bind it to the domain on port 443. So what I would like to know: How can I exept a domain from renewing the certificates with LetsEncrypt certificates? I already tried to delete it in the certificate console and all files with domain*.* below C:\Users\Administrator\AppData\Roaming\letsencrypt-win-simple\httpsacme-v01.api.letsencrypt.org But after 3 months all is back again an my customers cert is unbind. I don't know if it matters to delete and recreate the site in IIS - I did not already tried. Would be great to get a workaround from you! Best regards
Niko
# re: Using Let's Encrypt with IIS on Windows
@Niko - LetsEncrypt won't renew domains that you haven't set up with LetsEncrypt in the first place. So if LetsEncrypt is trying to update that domain you must have set up a certificate at some point.
Using Win Acme (formerly Lets Encrypt Win Simple) there's an option to show all managed certificates and to remove specific domains from the renewal cycle.
# re: Using Let's Encrypt with IIS on Windows
Hi Rick, thank you for that reminder!! I found a memo.txt with that information below. #2 and #3 I already did and now I also picked out the lines from the registry key under #1, regards Niko
#1 In the registry, HKEY_CURRENT_USER\Software\letsencrypt-win-simple\https://acme-v01.api.letsencrypt.org/, edit the key "Renewals" and delete the line(s) corresponding to the certificate(s) you don't want to renew. #2 In the C:\Users\USER\AppData\Roaming\letsencrypt-win-simple\httpsacme-v01.api.letsencrypt.org directory, delete all files associated with this certificate(s). #3 In MMC.exe, plugin "Certificates" (Computer), "webhosting" node : delete the certificate(s)
# re: Using Let's Encrypt with IIS on Windows
Awesome guide. I had to tinker with it a bit, but eventually got it working. One tiny (big) problem though. I was unable to run Visual Studio on the localhost in debug mode. It seems the installed cert was interfering with the dev cert provided with IIS Express. I tried everything Google told me to try, but no matter what, I keep getting the error "SSL_ERROR_RX_RECORD_TOO_LONG"
I found a workaround in this thread https://stackoverflow.com/questions/19417219/ssl-connection-connection-reset-with-iisexpress
Basically you turn off SSL for debugging, modify your URL rewrite rule in the web.config, and change the debug localhost port number to 44300. Weird, huh?
# re: Using Let's Encrypt with IIS on Windows
I have used Win-Simple on my webserver for years, thanks to the article published here by you, Rick! Now there is an update for the software of my mail server (other machine) running "MDaemon" regarding Let'sEncrypt, the statement (below) has been made and I am now wondering, if something similar for the installation on my webserver, where I use the (Win-Simple method), could be relevant? Do I have to make changes in near furture?
<< The features for LetsEncrypt have been updated to use ACME v2. This update became necessary because LetsEncrypt will stop supporting ACME v1. To use LetsEncrypt, PowerShell 5.1 and the .NET Framework 4.7.2 are now required.
# re: Using Let's Encrypt with IIS on Windows
LetsEncrypt-Win-Simple is now WinAcme which is the same tool just re-branded. I think you can just upgrade your older version to use the newer one and it'll pick up all your sites and continue to work with it - you'd just have to renew all your certificates.
# re: Using Let's Encrypt with IIS on Windows
Thanks for your post, so interesting for me. I have approximately 100 sites hosted with my IIS windows machine.
I don't have anyone SSL at the moment because of the cost and the amount of work/management involve.
do you expect any problems using let's encrypt for all of them?
Great article! Thank you 😃
# re: Using Let's Encrypt with IIS on Windows
@maxime - no LetsEncrypt should work for all of them. But be aware that there are some same domain limits - you can only create so many same domain certificates in a given timeframe. Separate domains are not an issue though - you can do as many as you want. I suggest staggering the domains as much as possible (ie. don't do them all at once but space out over a few days). This will help spread the load over a wider block of time.
# re: Using Let's Encrypt with IIS on Windows
Just wanted to say that i have always enjoyed your posts. You keep everything at a level that's easy to read. I'm pretty well "versed" in IT in general, and doing software development and Cloud architecture, but sometimes all the articles i read, is well written, but to "heavy" for light reading. You always keep it simple and to the point, so good job 👍 😃
# re: Using Let's Encrypt with IIS on Windows
Hi Rick,
I've been a fan of West-Wind and you going all the way back to the dev conferences that Will hosted in Milwaukee and SouthWest Fox in Gilbert. I've attended all of you workshops in every conference that I attended (5-6), that you have spoken at and I have learned so much. And thanks for continuing to share.
If I'm hosting www.domain.com and mail.domain.com on 2 different servers (both Windows 2016 Web Server and Windows 2016 Exchange Server), would the hassle outweigh the benefits since renewalls cannot be automated and expires too quickly?
I understand I can automate one of them (say the, www server), but the other server (exchange) would have to be manually renewed by creating a MyKey.pfx file containing both public and private keys using Window's export and import routines from cert manager on the www server and importing it into the exchange server.
Some info about our setup for use with LetsEncrypt... We use host headers with a single ip address and SAN certs currently, and I always cringe to think about a cert name change to the san cert and renew all related sites. All sites hosted on the IIS server has their mail counterpart hosted on a separate mail server. Some sites are hosting ftp and they are on their own ftp server.
Am I understanding this correctly? If not, please explain how I can automate and use this as the savings in time and cash are great.
Another related question... You or someone mentioned that it is standard practice to add www.domain.com, mail.domain.com, ftp.domain.com, sales.domain.com to the LetEncrypt cert. Normally when getting a san with a long list of domains that will be added to the cert, would the www. subdomain need to be added as many authorities would use it (www.) as the CN (common name) and would not be included in the domain list. So, does LetsEncrypt use the CN schema?
Thanks, Stanley
# re: Using Let's Encrypt with IIS on Windows
@Stanley - not sure what you're asking exactly. Domain validation by lets encrypt occurs by individual subdomain not to the top level domain. Meaning you can register d1.domain.com and d2.domain.com on different machines. If you use WinAcme you'll want to be doing that anyway because WinAcme handles the renewal and adding to IIS. So you basically set up WinAcme on each server that needs it then run the domain registration and the auto-renewals will handle via scheduled task that fires once a day and checks for updates.
# re: Using Let's Encrypt with IIS on Windows
Hi Rick,
So I would deal with the specific sub/domains for each and every machine independently, without regard to any other machine? And if I need to use a specific cert for a specific machine elsewhere, I would need to export it from the registered machine with the key for use on other machines. In other words, the machine registering it can be made to automatically update itself while all other machines that needs that cert would have to be manually exported and imported into the other non-registered machines?
So wouldn't I have to manually update all the other machines that requires the cert to that site such as FireFox (which immediately comes to mind) on the other machines? If so, then having to do this on many machines every 2-3 months could raise the hassle factor too high, correct?
Thanks, Stanley
# re: Using Let's Encrypt with IIS on Windows
So what is your use case here? You can't really have multiple machines with the same domain name? The only scenario I can see there is a load balanced cluster, but then you probably will have some sort of front end proxy that handles the incoming secure connection and forwards to the backends over plain http (or self-signed certs)...
# re: Using Let's Encrypt with IIS on Windows
Hello Rick, great work on Let's encrypt ... I use it on my 4 domains with auto-update and it work really well . I think for non-commercial , startup and even for small businesses this is the way to go ... sometime small business owner who want a site dont understand very well that a domain name is not all what is needed, but on top developping the site come hosting fee , now SSL if you want any chances to be showing in a Search Engine .. so to be able to get a low cost/free certificate is obviously welcome ... cheer.




# re: Using Let's Encrypt with IIS on Windows